Helo everyone, at the previous article I’ve been discuss about SSH restriction access, Now let’s going to the next challege.
In this tutorial based on SSH restriction topics, I’ll continue to make the remote access policy more strict.
The policy is when the users with permit remote access is failure login 3 times within 60Seconds, It will blocked the remote access temporary based on time period. in this case I’ll automatic disable SSH connection in 2 minutes (120sec).
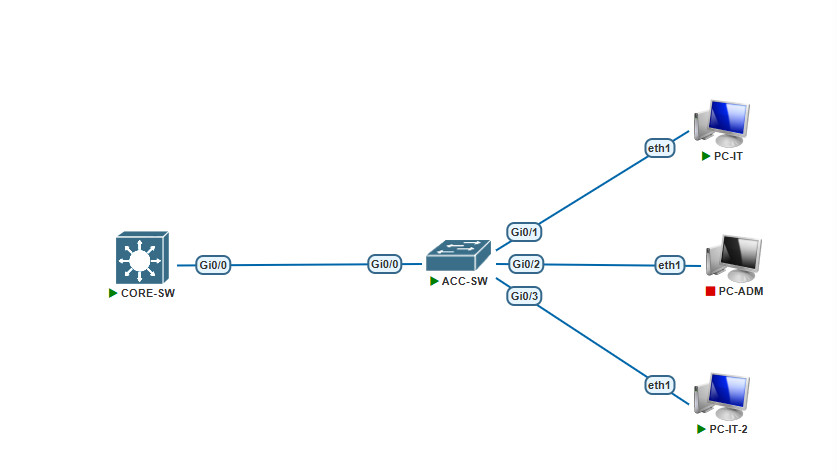
I’ll use existing topology & config with addition PC-IT for testing.
First configure ACL to specify Blocking rule for remote access :
CORE-SW(config)#ip access-list extended BlockACL
CORE-SW(config-ext-nacl)#50 deny tcp any any eq telnet CORE-SW(config-ext-nacl)#60 deny tcp any any eq www CORE-SW(config-ext-nacl)#70 deny tcp any any eq 22 CORE-SW(config-ext-nacl)#80 permit ip any any CORE-SW(config-ext-nacl)#exit
Note : For the configuration above it start from 50 so if need a permit to spesific IP after config you can add to lower sequence number.
Configure login block parameter to provide DoS detection. It will blocked for 2 minutes when user doing a 3 times login failure attempt within 60sec (1minutes).
CORE-SW(config)#login block-for 120 attempts 3 within 60
Configure login quiet-mode to specify the ACL Rule when the switch device is switches to quiet-mode. Note that when the switch is in quiet-mode, all login request will be denied and only available through the console.
CORE-SW(config)#login quiet-mode access-class BlockACL
Configure login delay to add a delay between successive login attempts.
CORE-SW(config)#login delay 10
After that verify the config
CORE-SW#show login A login delay of 10 seconds is applied. Quiet-Mode access list BlockACL is applied. Router enabled to watch for login Attacks. If more than 3 login failures occur in 60 seconds or less, logins will be disabled for 120 seconds. Router presently in Normal-Mode. Current Watch Window remaining time 9 seconds. Present login failure count 0. CORE-SW#
As the shown above, the configuration is appropriate. the Switch is in Normal-Mode
Now time to user test :
I’m trying to make 3 failure login attempts. after 3 times failure, as shown bellow remote connection toward CORE switch will be blocked, other connection like ping typeor etc is still in normal.

Here’s the log from Switch side when the CORE is detected login failures and switches from Normal-Mode to the Quiet-Mode
CORE-SW# *Jul 19 17:44:37.099: %SEC_LOGIN-1-QUIET_MODE_ON: Still timeleft for watching failures is 38 secs, [user: ] [Source: 172.16.100.2] [localport: 22] [Reason: Login Authenticati on Failed] [ACL: BlockACL] at 17:44:37 UTC Sat Jul 19 2025 CORE-SW#
Verify show login, as shown below CORE switch has switches to Quiet-Mode for 2 minutes.
CORE-SW#show login A login delay of 10 seconds is applied. Quiet-Mode access list BlockACL is applied. Router enabled to watch for login Attacks. If more than 3 login failures occur in 60 seconds or less, logins will be disabled for 120 seconds. Router presently in Quiet-Mode. Will remain in Quiet-Mode for 119 seconds. Restricted logins filtered by applied ACL BlockACL. CORE-SW#
You can also known which user ip that has3 times login failures.
CORE-SW#show login failures Information about last 50 login failure's with the device Username SourceIPAddr lPort Count TimeStamp taufik 172.16.100.2 22 3 17:44:37 UTC Sat Jul 19 2025 CORE-SW#
Now verify and try to remote access the CORE switch from PC-IT-2. The result is remote connection is also Blocked because switch is in Quiet-Mode. So you need to waiting for until the CORE is switch back to Normal-Mode or you can access via Console.
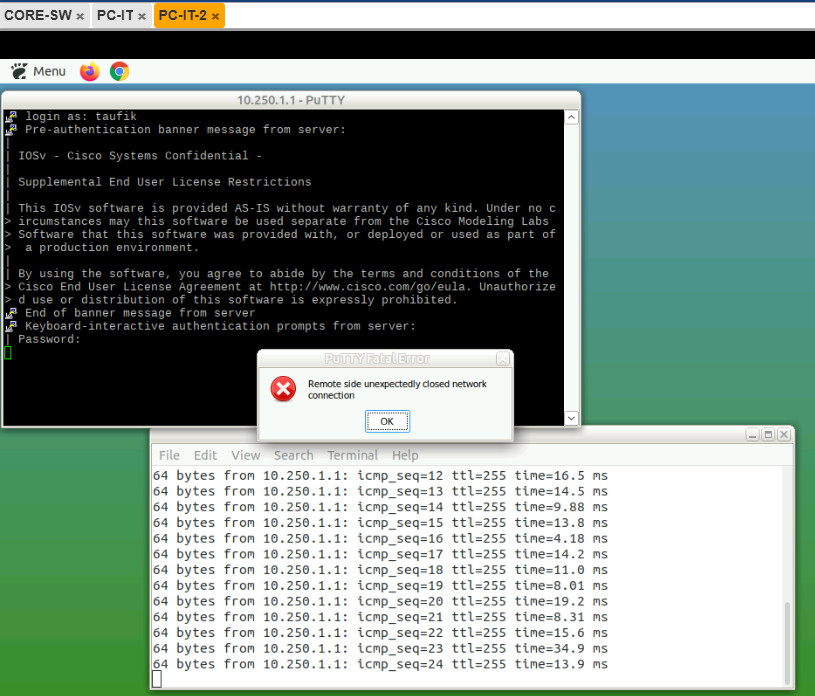
Here’s the log from CORE switch when there is client try to connect to switch/router in Quiet Mode active.
CORE-SW# *Jul 19 17:45:52.124: %SEC_LOGIN-1-QUIET_MODE_ON: Still timeleft for watching failures is 0 secs, [user: ] [Source: 172.16.100.3] [localport: 22] [Reason: Login Authentication Failed] [ACL: BlockACL] at 17:45:52 UTC Sat Jul 19 2025 CORE-SW#